Our team thought it would be a good idea to add a glossary with terms you will come across on this blog. We hope these terms will enhance your learning experience. We’ve done our best to simplify these terms and find credible sources you can refer to. Since this glossary will be constantly growing, we welcome your help in identifying terms you would like us to simplify, so just comment the term below!
Artificial Intelligence: Replication of human intelligence in machines. “ It is the science and engineering of making intelligent machines, especially intelligent computer programs.” – John McCarthy (founding father of AI)
Bitcoin: Is a type of cryptocurrency which users send to each other on a peer to peer network. The peer to peer network is supported by distributed ledger technology like the blockchain.
To learn more about bitcoin and the technology visit: https://bitcoin.org/en/how-it-works
Blockchain: A technology where a virtual ‘block’ consisting of private data is stored in a virtual public space ‘chain’. The ‘block’ is made up of pieces of information like transaction details – purchases, game assets, cryptocurrency, domain names and more. Each block contains a hash which protects the data and prevents tampering of the data. The blockchain resembles a virtual distributed ledger which is shared on a public network – this prevents false transactions.
Watch this video to learn more about blockchain and how it works! https://www.youtube.com/watch?time_continue=81&v=27nS3p2i_3g&feature=emb_logo or https://www.youtube.com/watch?v=SSo_EIwHSd4
Cryptocurrency: Is virtual currency protected by cryptography making it impossible to replicate/counterfeit.
Cybersecurity: Policy and framework which resolves to protect individuals, institutions and entities from various threat actors and cyber attacks.
Cyber Warfare: Cyber Warfare may be defined as the use of technology, by countries or terrorist organisations to attack or disrupt a country’s information network to protect themselves, or weaken a country’s ability to fight. Cyber Warfare can severely affect a country’s military, or intelligence operations during or before the time of conflict.
For reading more on Cyber Warfare, please check out this website: https://www.rand.org/topics/cyber-warfare.html
Cyber Terrorism: Cyber Terrorism maybe defined as the violent use of internet to cause severe monetary, physical or bodily harm; or to threaten non-combatants or civilians, organisations or commercial units, to pursue political or ideological goals through the use of internet for causing intimidation and fear.
For reading more on Cyber Terrorism, please check out this link: https://www.nato.int/structur/library/bibref/cyberterrorism.pdf
Deep Learning: A subset of machine learning, deep learning is when computers are programmed to resemble and act like a network of neurons in the human brain. It imitates the function of neurons to form an artificial neural network within computers and machines allowing them to process information and perform functions which could earlier only be done by specific manual coding. ‘Deep’ refers to the various layers at which information is identified and processed. The learning process itself can be supervised, un-supervised or semi-supervised.
Watch this video to understand the nuances between AI, Machine Learning and Deep Learning! Deep Learning Vs Machine Learning | AI Vs Machine Learning Vs Deep Learning
Digital Signatures: The digital equivalent of physical signatures that tie the identity of an individual to the rendering of an electronic document/record into an authentic one.
For a more detailed explanation of how digital signatures work, one can check out this video: https://www.youtube.com/watch?v=JR4_RBb8A9Q
DLT or Distributed Ledger Technology: Is a digitised ledger (book of records of transactions etc). This digital ledger records and replicates the data in multiple virtual spaces at the same time. It is a publicly shared ledger which operates on a peer-to-peer network. Since it has no central storage centre but is spread across various databases, the falsification and corruption of the data is impossible.
Watch this video to understand the mechanics of DLT https://www.youtube.com/watch?v=Cqk7PN8f8gM&t=116s
Encryption: Is a concept of cryptography, wherein an algorithm scrambles ‘encrypts’ data into an alternative form which is unscrambled or ‘decrypted’ with a key.

Symmetric Encryption

Where one private key is used code and decode the data. This method is faster as only one key is used by sending and receiving party, however the transmission of the key can be risky.
Say Sherlock wants to send Watson an important document he found during a crime investigation. Sherlock secures the information in an online document and locks it with a virtual encryption key. He sends the document by email to Watson, however Watson can only unlock the document with the same key that Sherlock locked it with. So Sherlock has to send another email with the key. This is risky as a hacker can easily gain access to the document and the key in the same inbox!
Asymmetric Encryption

This encryption uses a public and private key. This is far more secure method of encryption as the document’s can only be unlocked by a private key. Both private & public keys must be read together.
Let’s again take Sherlock and Watson’s example, except that this time there are two keys – a public key and a private key. Since Sherlock wants to send Watson the information, he will lock the data with Watson’s Public Key, which Watson had sent him earlier. Then Sherlock emails the secured document and Watson will unlock the document with Watson’s Private Key. If Watson wants to send information back to Sherlock, then he will lock the information with Sherlock’s Public Key and Sherlock will unlock it with his own Private key. Essentially there are 4 keys in this transaction (i) Watson’s public key (ii) Watson’s Private Key (iii) Sherlock’s Public Key and (iv) Sherlock’s Private key.
Founding Fathers: Professor John McCarthy, Alan Turing, Marvin Minsky, Allen Newell, and Herbert A. Simon.
Hash or Cryptographic Hash: Is the usage of hash function to secure communication. The hash algorithm converts/digests the data into a unique code which is irreversible. To unlock the information, the end user requires a unique key which can unlock that particular code.
Information Warfare: Information Warfare (IW) may be defined as the exploitation of information domain to attack or weaken an adversary’s ability to fight. IW is an umbrella term which includes operations carried out in the information environment by state and non-state actors to disrupt, deny or corrupt military, government or other vital information, by or through the use of electromagnetic domain.
For a more detailed explanation of Information Warfare, please check out this document: https://www.hsdl.org/?view&did=443229
For understanding the Information Warfare in the contemporary world, please check out this blog: https://www.weforum.org/agenda/2015/12/what-is-information-warfare/
Machine Learning: It is the study of computer algorithms that improve automatically through experience. The idea behind machine learning is that the machine can learn with least human intervention. It involves computers discovering how they can perform tasks (without being explicitly programmed to do so) by the help of the data provided. It is a subset of Artificial Intelligence.
| Supervised Learning | Un-supervised Learning | Semi Supervised Learning |
| Both Input and Output is fed in the program such that the data acts as a trainee for the network and helps predicting results. Since the machine has to be taught and fed information, a data scientist is usually present to oversee this process. | The Input/Raw data is processed with the help of algorithms used to identify various patterns based on observations. | Unlike Supervised or Unsupervised learning this process does not depend solely on one type of database but instead uses both labeled and un-labeled data during training. This means that the algorithm has an idea of what the output should look like but is not necessarily told how to arrive at the output. |
| Example | Example | Example |
| A professor teaching students in a classroom (virtual or physical) is a classic example of Supervised Learning. There is direct supervision of the professor over the students as he/she/they take the class. | Unsupervised Learning, could be seen in a situation where a student has maybe missed out on a class. The student borrows notes from a classmate and tries to learn on their own from the notes (given data set). | Homework is a perfect example of semi-supervised learning, where a professor after teaching the subject-matter in class will give the students an assignment on the topic. Thus when the student does the homework, they apply the concepts they learnt on their own and attempt to arrive at the answer. |
Malware: Malicious software, or malware is a software used by attackers to cause damage to computer systems and networks. Malware includes viruses, worms, spyware and ransomware, amongst others.
For a more detailed overview of malware and how different types work, do watch this video published by Dell: https://www.youtube.com/watch?v=tKZBf-WNM8Y&ab_channel=DellSupport
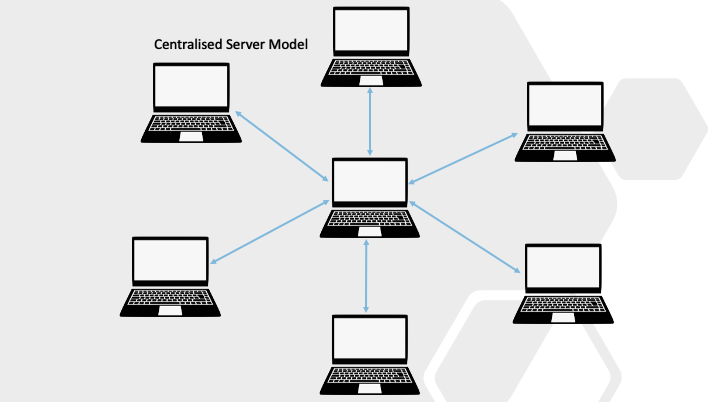
Peer to peer: A P2P network is a system where each computer in the network are connected to each other directly rather than through a central server. This allows files and data to be shared directly among the computers. DLT and blockchain relies on this mode of networking so that data is stored simultaneously on multiple servers rather than on a single server.

Sources:
- https://blockgeeks.com/guides/what-is-blockchain-technology/
- https://bitcoin.org/en/how-it-works
- http://jmc.stanford.edu/artificial-intelligence/what-is-ai/index.html
- AI vs Machine Learning vs Deep Learning: What’s the Difference?
- What is Malware”, CISCO, https://www.cisco.com/c/en/us/products/security/advanced-malware-protection/what-is-malware.html#~types-of-malware
- “What is Malware, How Malware Works and How to Remove it”, AVG, https://www.avg.com/en/signal/what-is-malware
Disclaimer: The definitions provided in this glossary have been collated by our Team and may not be entirely accurate or illustrative of the terms. This information is provided to our users to enhance understanding of the content on our blog and is in only meant for educational purposes.

[…] You may also like: Data Protection in a Globalizing World. […]
lush! 94 2025 IT Rules 2021: Much ado about nothing? A critical review and the problems on field in the…
supreme! 71 2025 IT Rules 2021: Much ado about nothing? A critical review and the problems on field in the…
Thank you for sharing this valuable information. I really enjoyed reading your post and gained some new insights on [topic].…
[…] The Drone Regulations 2021: One Step Forward and Two Steps Back – The Digital Future, accessed on June 19,…